39C3: Power Cycles
39C3: Power Cycles
I got back from the 39th Chaos Communication Congress in Hamburg. Brain still buzzing.
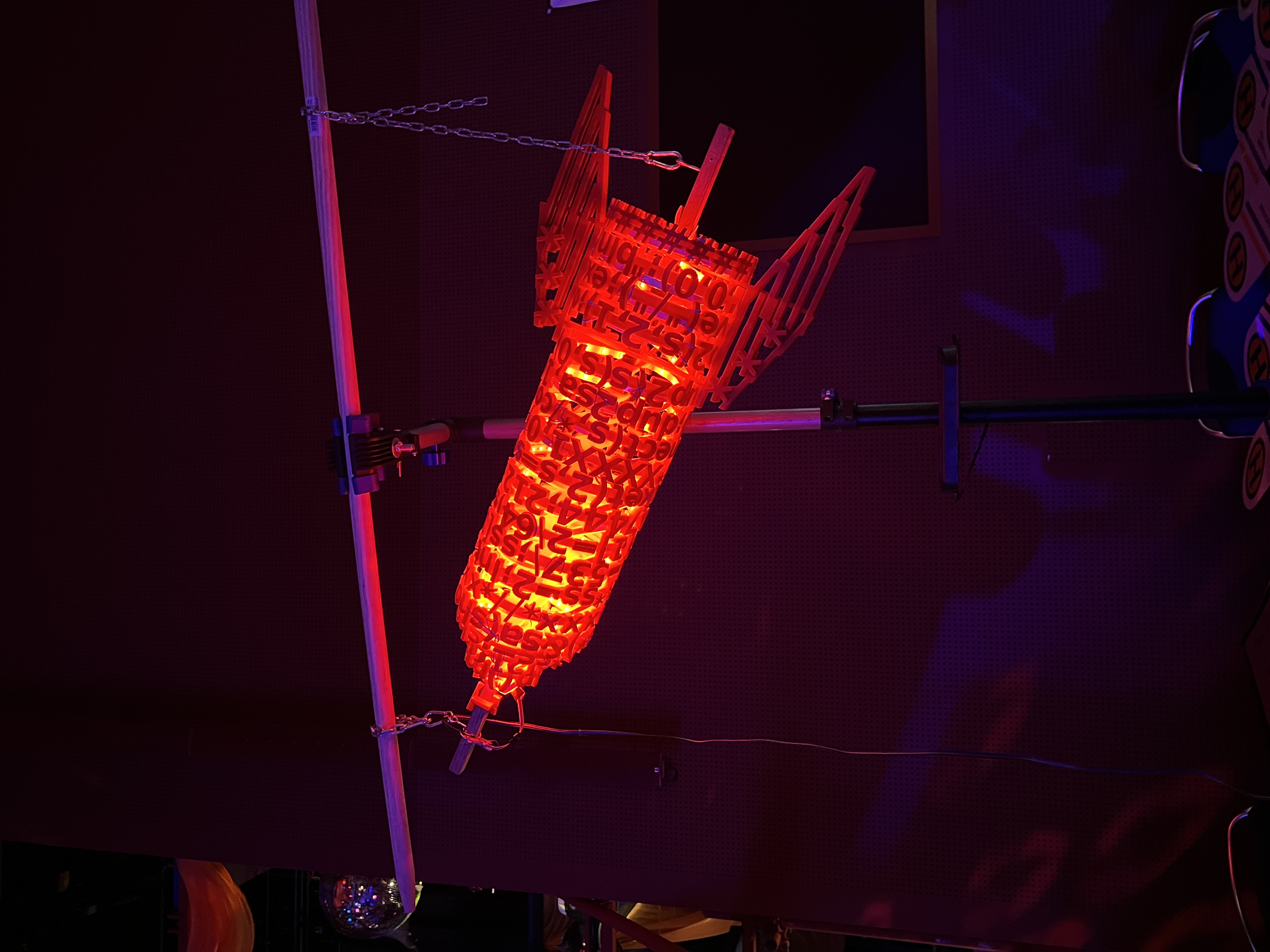
39C3 sold out all 16,000 tickets. The theme was “Power Cycles,” a nod to both electrical circuits and the cyclical churn of geopolitical order.
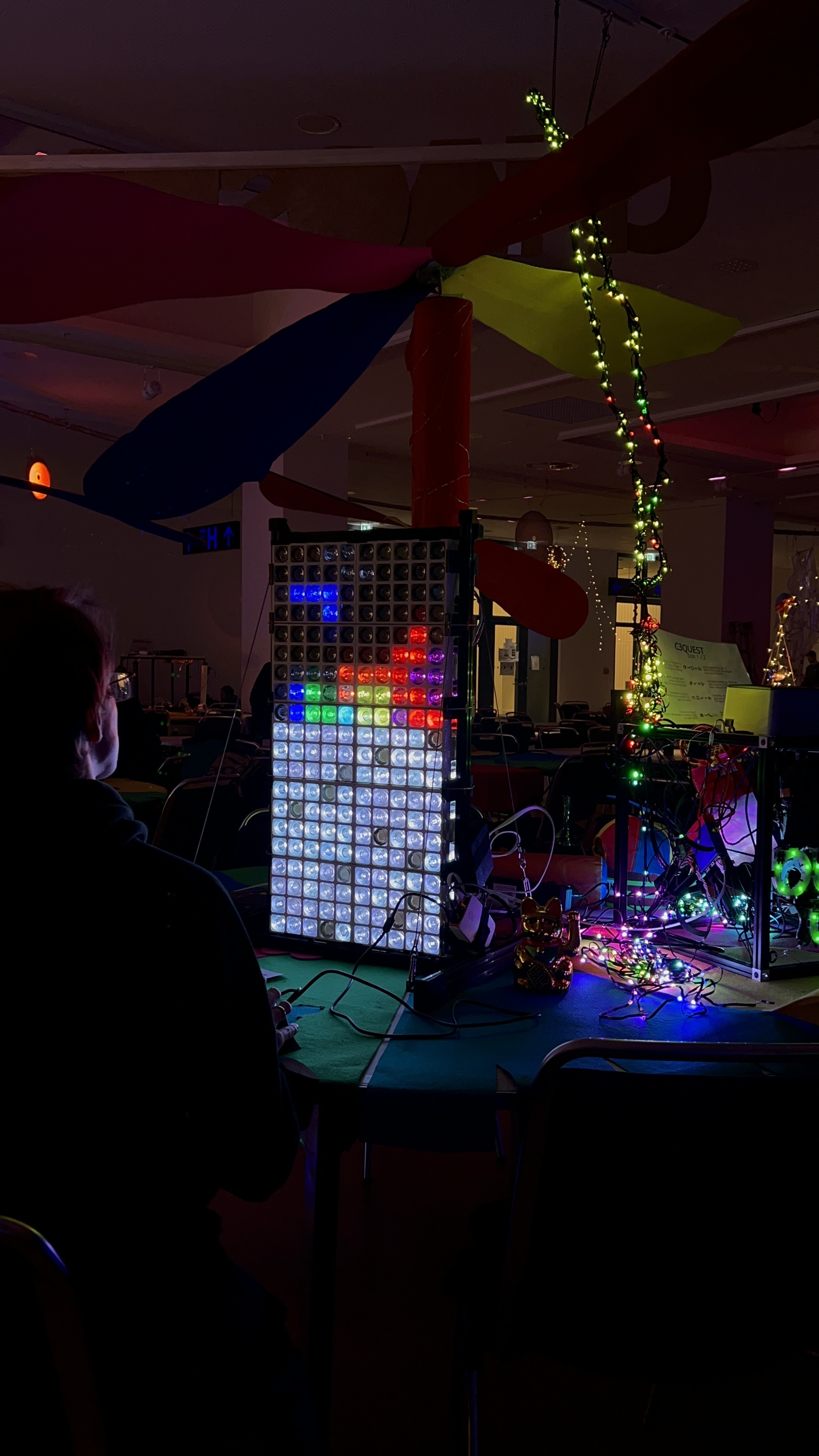
It’s hard to explain what Congress feels like to someone who hasn’t been. Think 4 days of security research, political talks, art installations, punk shows, soldering workshops, and hallway conversations that accidentally teach you more than the talks themselves. Every year feels different. This year felt special.
All talks are up at media.ccc.de/c/39c3. Here’s what stuck with me.
Day 1

Breaching the Great Firewall
“A Tale of Two Leaks” opened the congress. Researchers exploited a memory vulnerability in China’s DNS injectors (they called it “Wallbleed”) and pulled traffic data from both inside and outside the firewall. They basically turned China’s surveillance infrastructure against itself. The Geedge network part came from a leaked 600GB dump of GFW source code from a Chinese cybersecurity firm.
Surveillance tools have bugs too.
The Hardware Itch
A session on building hardware stripped away all the mystique. The presenter broke down how accessible it’s become to design and manufacture your own boards. I haven’t touched a soldering iron in years, but this talk lit something up (more on that later).
Meds, Money, and the Patent Cliff
One of the most surprising talks had nothing to do with code. A medicine costing $1 to $5 to produce often sells for ~$1,000 in the US (vs ~$100 in Europe). The gap is almost entirely patents.
The good news: 20% of those patents expire in the next 5 years. Expect prices to crater for several major drugs.
Hacking Washing Machines
Highlight of the day. Researchers reverse-engineered Miele and B/S/H firmware using optical bicommunication (yes, reading data through light pulses). They bolted together a chain of tools that lets you control Miele washing machines through the BSH app.
Your laundry is not safe.
Bluetooth Headphone Jacking
This demo was genuinely terrifying. Researchers extracted memory from Sony Bluetooth headphones, then impersonated the headphones to call Siri from a laptop.
The full kill chain: impersonate headphones, trigger Siri, make a call, answer incoming WhatsApp call (login code), take over WhatsApp, request Amazon login code via WhatsApp. Full account takeover. From a pair of Sony headphones.
Day 2
Don’t Look Up (It’s Unencrypted)
Classic CCC energy. A team built a parabolic dish to eavesdrop on GEO satellites. Unsurprisingly, they found mountains of unencrypted traffic.
The kicker: some mobile providers encrypted traffic between the phone and the cell tower, but treated satellite backhaul as a trusted internal network. Everything sent in the clear.
They picked up unencrypted Mexican military communications, including GPS coordinates of helicopters.
The assumption that “nobody can hear us up there” is spectacularly wrong.
Chinese App Crypto (or Lack Thereof)
Not recorded.
WeChat rolls its own encryption protocol (mmtls) instead of standard TLS. Many Chinese IME apps (the software that lets you type Chinese characters on a small keyboard) use cloud-based predictors that send your keystrokes over plain HTTP.
Researchers built scrapers for Chinese app stores, used a tiny LLM to click through the apps, and sniffed for unencrypted connections. Result: ~50% of apps were leaking data.
Robot Jailbreaks
The “Skynet Starter Kit” talk: researchers bought a cheap Unitree “AIR” robot dog and jailbroke it. Hilarious and unsettling. Embodied AI is coming, and it’s about as secure as your Wi-Fi connected toaster.
Day 3

AI Agent, AI Spy
This one hit close to home. The talk argued that the shift from traditional OS tools to agentic systems opens the door to active surveillance.
The core problem: prompt injection can instruct an AI agent to use its own legitimate tools to exfiltrate credentials. The agent sees a valid request from an authorized source. It complies. This is the Confused Deputy Problem, and it’s probably unsolvable in current LLM architectures.
The $151k CPU Bug
Google paid $151,151 for this one. A CPU vulnerability that bypasses VM isolation in cloud environments. The presenter demoed leaking a private key from a victim’s VM (running nginx) by exploiting shared physical hardware.
Cloud providers pack multiple customer VMs onto the same CPUs. The isolation is supposed to be airtight. It wasn’t.
Day 4
AI Speed-Running Defense
The congress closed with “Breaking BOTS,” about using AI to speed-run Blue Team CTFs. They wired Claude Code into Splunk to automate security investigations.
If defenders are automating with AI, attackers already are too.
Soldering: The Unexpected Highlight
I didn’t expect this to be the thing I kept thinking about after Congress. But here we are.
Between the hardware talk on Day 1 and the soldering workshops scattered across the venue, something clicked. Congress had soldering stations set up where you could sit down, grab a kit, and just build. There’s something deeply satisfying about a physical thing you assembled with your hands actually working. No deployment pipeline, no CI, no YAML. Just flux, solder, and a blinking LED.
I bought a couple of soldering kits before I left Hamburg. I’m planning to work through them at home and get back into hardware projects. Congress has a way of reminding you that building things with your hands is incredibly satisfying.
Final Thoughts
The same cracks keep showing up year after year: unencrypted data where it shouldn’t be, memory safety bugs in critical infrastructure, blind trust in hardware isolation. The tools get fancier. The mistakes stay the same.
I’m leaving with a reading list, a couple of soldering kits, and the itch to build something with my hands.
See you at 40C3.